Funny how CrowdStrike already sounds like some malware’s name.
It literally sounds like a DDoS!
Botnet if you will
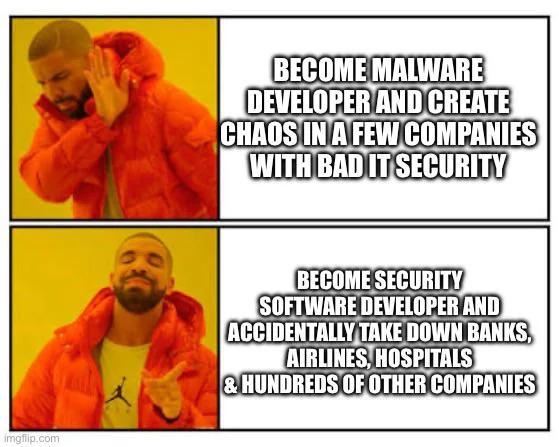
Not too surprising if the people making malware, and the people making the security software are basically the same people, just with slightly different business models.
This is, in a lot of ways, impressive. This is CrowdStrike going full "Hold my beer!" about people talking about what bad production deploy fuckups they made.
You know you’ve done something special when you take down somebody else’s production system.
*production systems around whole world
I'm volunteering to hold their beer.
Everyone remember to sue the services not able to provide their respective service. Teach them to take better care of their IT landscape.
Typically auto-applying updates to your security software is considered a good IT practice.
Ideally you'd like, stagger the updates and cancel the rollout when things stopped coming back online, but who actually does it completely correctly?
Applying updates is considered good practice. Auto-applying is the best you can do with the money provided. My critique here is the amount of money provided.
Also, you cannot pull a Boeing and let people die just because you cannot 100% avoid accidents. There are steps in between these two states.
you cannot pull a Boeing and let people die
You say that, but have you considered the savings?
People are temporary. Money is forever.
I have. They are not mine. The dead people could be.
Edit: I understand you were being sarcastic. This is a topic where I chose to ignore that.
That's totally fair. :)
I work at a different company in the same security space as cloudstrike, and we spend a lot of time considering stuff like "if this goes sideways, we need to make sure the hospitals can still get patient information".
I'm a little more generous giving the downstream entities slack for trusting that their expensive upstream security vendor isn't shipping them something entirely fucking broken.
Like, I can't even imagine the procedureal fuck up that results in a bsod getting shipped like that. Even if you have auto updates enabled for our stuff, we're still slow rolling it and making sure we see things being normal before we make it available to more customers. That's after our testing and internal deployments.
I can't put too much blame on our customers for trusting us when we spend a huge amount of energy convincing them we can be trusted to literally protect all their infrastructure and data.
The real malware is the security software we made along the way.
We've known that since Norton and McAfee.
At least McAfee's antics were entertaining
The answer is obviously to require all users to change their passwords and make them stronger. 26 minimum characters; two capitals, two numbers, two special characters, cannot include '_', 'b' or the number '8', and most include Pi to the 6th place.
Great! Now when I brute force the login, I can tell my program to not waste time trying '_', 'b' and '8' and add Pi to the 6th place in every password, along with 2 capitals, 2 numbers and 2 other special characters.
Furthermore, I don't need to check passwords with less than 26 characters.
What’s the saying about dying a hero or becoming the villain?
ItS NoT A wInDoWs PrObLeM -- Idiots, even on Lemmy
I genuinely can't tell at whom you are addressing this. Those claiming it is a Windows problem or those that say otherwise?
You can not like windows, and also recognize that CrowdStrike isn't from Microsoft - so a problem that CrowdStrike caused isn't the fault of Windows.
If that makes me a idiot by holding two different ideas in my head, so be it, but you are spending time with us, so thank you for elevating us!
I'm sorry, but distinguishing between different concepts is forbidden here. You go straight to jail.
Hi, idiot here. Can you explain how it is a windows problem?
It's a problem affecting Windows, not problem caused by Windows I guess.
If you patch a security vulnerability, who's fault is the vulnerability? If the OS didn't suck, why does it need a 90 billion dollar operation to unfuck it?
Redhat is VALUED at less than that.
https://pitchbook.com/profiles/company/41182-21
It's a fucking windows problem.
Sure, but they weren't patching a windows vulnerability, windows software, or a security issue, they were updating their software.
I'm all for blaming Microsoft for shit, but "third party software update causes boot problem" isn't exactly anything they caused or did.
You also missed that the same software is deployed on Mac and Linux hosts.
Hell, they specifically call out their redhat partnership: https://www.crowdstrike.com/partners/falcon-for-red-hat/
Crowdstrike completely screwed the pooch with this deploy but ideally, Windows wouldn’t get crashed by a bas 3rd party software update. Although, the crashes may be by design in a way. If you don’t want your machine running without the security software running, and if the security software is buggy and won’t start up, maybe the safest thing is to not start up?
Are we acting like Linux couldn't have the same thing happen to it? There are plenty of things that can break boot.
CrowdStrike also supports Linux and if they fucked up a Windows patch, they could very well fuck up a linux one too. If they ever pushed a broken update on Linux endpoints, it could very well cause a kernel panic.
Yeah, it's a crowd strike issue. The software is essentially a kernel module, and a borked kernel module will have a lot of opportunities to ruin stuff, regardless of the OS.
Ideally, you want your failure mode to be configurable, since things like hospitals would often rather a failure with the security system keep the medical record access available. :/. If they're to the point of touching system files, you're pretty close to "game over" for most security contexts unfortunately. Some fun things you can do with hardware encryption modules for some cases, but at that point you're limiting damage more than preventing a breach.
Architecture wise, the windows hybrid kernel model is potentially more stable in the face of the "bad kernel module" sort of thing since a driver or module can fail without taking out the rest of the system. In practice.... Not usually since your video card shiting the bed is gonna ruin your day regardless.
"even on Lemmy"
Like this is some highbrow collection of geniuses here?
Because it isn't. Their Linux sensor also uses a kernel driver, which means they could have just as easily caused a looping kernel panic on every Linux device it's installed on.
Maybe this is a case of hindsight being 20/20 but wouldn't they have caught this if they tried pushing the file to a test machine first?
It's not hindsight, it's common sense. It's gross negligence on CS's part 100%
I saw one rumor where they uploaded a gibberish file for some reason. In another, there was a Windows update that shipped just before they uploaded their well-tested update. The first is easy to avoid with a checksum. The second...I'm not sure...maybe only allow the installation if the windows update versions match (checksum again) :D
Now threat actors know what EDR they are running and can craft malware to sneak past it. yay(!)
Smart threat actors use the EDR for distribution. Seems to be working very well for whoever owned Solar Winds.
A real Anakin arc right here.
SHOULD'VE USED OPENBSD LMAO

Yes but the difference is one of them is also going to help you fix it.
Programmer Humor
Welcome to Programmer Humor!
This is a place where you can post jokes, memes, humor, etc. related to programming!
For sharing awful code theres also Programming Horror.
Rules
- Keep content in english
- No advertisements
- Posts must be related to programming or programmer topics